Security company finds some e-ticketing links exposed to hackers
10 February, 2019
3 min read
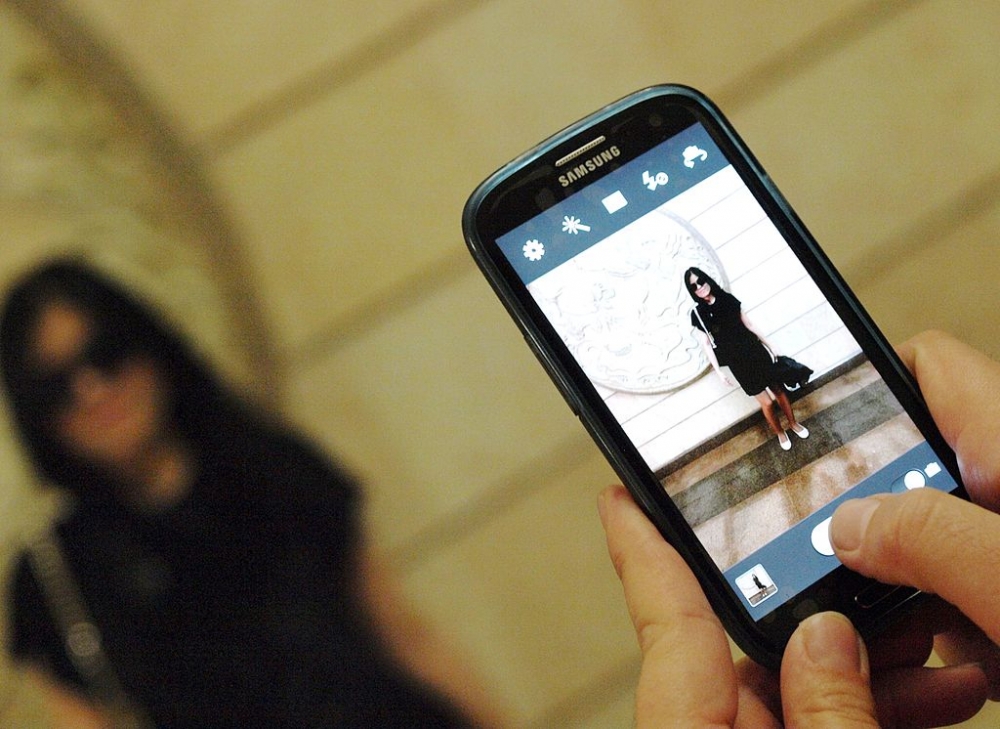
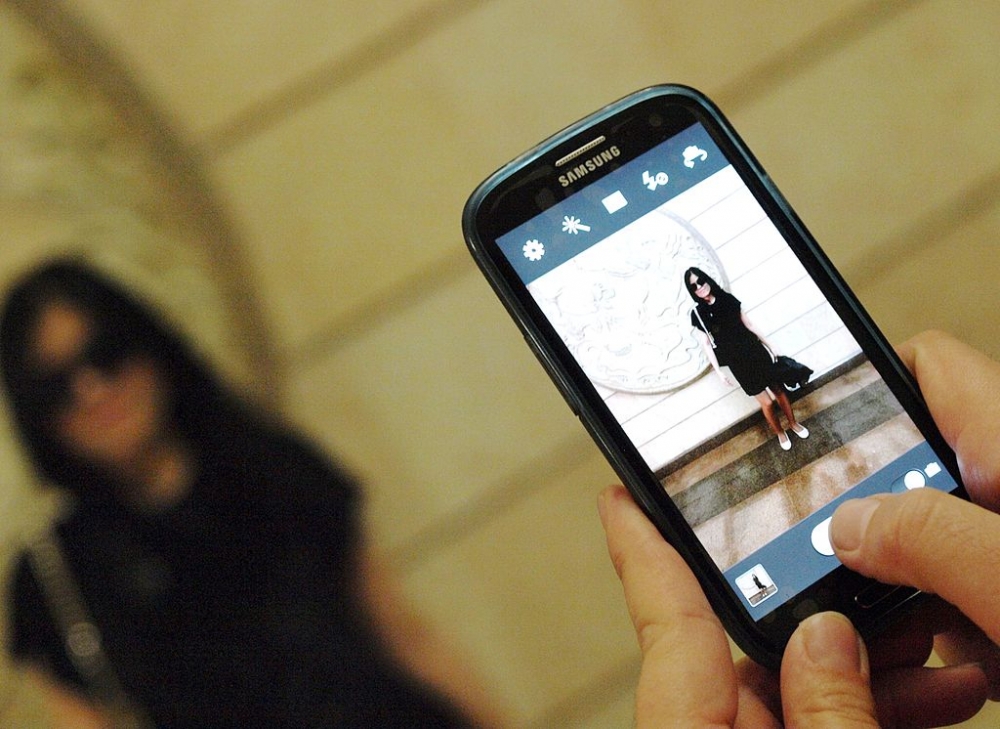
E-ticketing systems at some airlines are using unencrypted links that may expose customers' personal information to hackers, according to threat experts at mobile security company Wandera.
The company says the links can be easily intercepted by hackers and enable third parties to view, and in some cases change, a user’s flight booking details or even print a boarding pass.
Airlines identified by the researchers as sending unencrypted links included Australian low-cost carrier Jetstar, Southwest Airlines, Air France, KLM, Spanish budget carrier Vueling, British charter carrier Thomas Cook, Holland’s Transavia and Air Europa.
Air France and Jetstar have already said they have seen no evidence of misuse.
According to Wandera, hackers could use credentials in the links to visit the e-ticketing system at any point, even multiple times, prior to take-off.
It said potential data that could be exposed included email addresses, names, passport details, booking references, flight times, seat assignments, baggage selections, boarding passes and details of travel companies booking the flights.
However, it noted there were differences in the types of data exposed by each booking system it had investigated.
An anonymized list showing what information could be accessed indicated name and booking reference were the only details that could be accessed at one airline.
Details at the worst offender included gender, date of birth, nationality, passport/ID numbers and expiration date, frequent flyer number, email and mobile phone number.
The company identified the threat in December and said a hacker would not only be able to access personal information but in some cases add or remove bags, change seat allocation and change the mobile phone number and email associated with the booking.
“Recent reports of a man who was able to board the wrong flight raises questions about the varied quality of boarding pass screening at the gates of some airports,’’ it said.
READ: White knuckles at first 747 flight 50 years ago.
“ That is why the most concerning aspect of this vulnerability is the possibility for a hacker or criminal to print a victim’s boarding pass and attempt to board a scheduled flight.”
The company said it had shared its findings with government security agencies and recommended that airlines adopt encryption throughout the boarding process.
Air France said in a statement it was working on an enhanced security link.
It said its databases were monitored in real time to identify and prevent fraudulent access and had not been hacked.
“An e-mail sent to the customers before their trip contains a link to the check-in process on the airlines' commercial websites,’’ it said.
“Fraudulent use of this link would under no circumstances allow access to data other than that of the current reservation. Customer profile information, including sensitive information such as bank details, is fully protected.”
Jetstar also said it had seen no evidence of misuse.
“We take cybersecurity and privacy extremely seriously and have no evidence of our customers’ booking details or data ever being misused by unauthorized parties through the booking link,” the airline told iTnews
“To ensure our customers’ information remains protected we have multiple layers of security in place and are continuously implementing further cyber safeguards for emails, itineraries and our systems.
“Sensitive customer information such as payment details are not accessible through a customer’s booking link.”
Next Article
2 min read
Qantas triples profit but misses mark

Get the latest news and updates straight to your inbox
No spam, no hassle, no fuss, just airline news direct to you.
By joining our newsletter, you agree to our Privacy Policy
Find us on social media
Comments
No comments yet, be the first to write one.
